 Live Preview
Live PreviewKadag Security
Features
- Sandboxed Environment — Kadag Security runs your app in a secure, isolated environment, ensuring that tests do not affect your production systems.
- AI Security Agents — The tool employs advanced AI agents to monitor and analyze your app's behavior, providing insights into potential vulnerabilities.
- Automated Repo Cloning — With a simple command, Kadag Security clones your repository, making setup quick and hassle-free.
- Docker Compose Integration — It seamlessly spins up your application using Docker Compose, allowing for consistent and reproducible testing environments.
- Instrumented Environment — The app is placed in an instrumented environment, enabling detailed tracking and analysis of its performance and security posture.
- User-Friendly Interface — The intuitive interface makes it easy for developers to navigate and utilize the tool effectively, regardless of their technical background.
FAQ
What is Kadag Security?
This setup allows for a comprehensive assessment of your app's security posture, as it interacts with a suite of AI-driven security agents designed to identify vulnerabilities and potential threats in real-time. By simulating various attack vectors, Kadag Security provides developers with actionable
How much does Kadag Security cost?
Visit the official Kadag Security website for the most up-to-date pricing.
What are the key features of Kadag Security?
Kadag Security includes features such as: [object Object], [object Object], [object Object], [object Object], [object Object].
Related Tools
Tools with similar capabilities you might also like
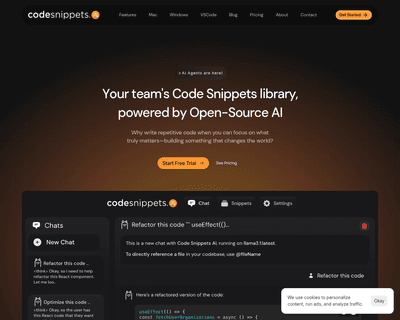
By integrating advanced AI models like GPT-4, Mixtral 8x7B, and Capybara 7B, it enables users to efficiently tackle code generation, refactoring, debugging, and

By offering a user-friendly platform, it allows individuals to easily access various AI capabilities, such as image and text analysis, machine translation, and

With tools like NeuralBox and NeuralCam Live, users can enjoy enhanced low-light photography and professional-quality video editing without needing extensive te

By systematically scanning public IP addresses and domain names, it gathers detailed information about the services and protocols in use, allowing users to iden

Its comprehensive features encompass automated API discovery, business logic security testing, and seamless integration with CI/CD pipelines, all designed to he

This flexibility allows organizations to optimize their GPU utilization without the need for code modifications, making it particularly appealing for teams alre